Multi-Chain Wallets Explained
Multi-chain wallets consolidate control of assets across diverse blockchains from a single interface. They offer streamlined access and unified exposure, yet introduce fragmented security and potential liquidity gaps. By coordinating cross-network actions, these wallets depend on layered validation, standardized messaging, and contingency aborts to manage risk. The custody model—whether hot, non-custodial, or bridge-based—shapes governance and accountability. The tradeoffs warrant careful consideration before adopting such solutions, as the next step may redefine how users protect and move value.
What Are Multi-Chain Wallets and Why They Matter
Multi-chain wallets are software solutions that manage assets across multiple blockchain networks from a single interface. They enable streamlined access, consolidated control, and diversified exposure, supporting user autonomy within a complex ecosystem. However, risks include fragmented security, liquidity gaps, and governance uncertainty. The concept of cross chain custody underscores responsibility division, emphasizing disciplined asset protection and clear accountability across networks, markets, and protocols.
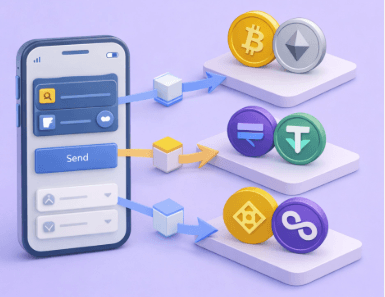
How Multi-Chain Wallets Work Across Networks
How do multi-chain wallets coordinate assets and actions across disparate networks without duplicating effort? They rely on coordinated event forwarding, standardized messaging, and cross-network state awareness to align commitments while preserving autonomy. Security models emphasize verification over trust, and cross chain risks are mitigated through layered validation, fail-safes, and contingency aborts. Systemic clarity underpins freedom with disciplined risk management.
Models and Tradeoffs: Hot vs. Non-Custodial, Bridges, and Integrations
Across interoperable ecosystems, practical choices define how assets are held, moved, and governed. Models range from hot wallets to non-custodial setups, each balancing control and risk.
Bridges enable cross-chain transfers but introduce security risks and potential liquidity gaps.
Integrations ease use yet concentrate points of failure, raising privacy implications and requiring deliberate risk assessment for freedom-minded users.
Practical Guidance for Safe Use and Best Practices
The discussion outlines structured steps to reduce exposure to security risks, emphasizing careful user onboarding, vigilance with seed phrases, and habit formation for routine verification.
It prioritizes clear routines, modular checks, and incident response to sustain autonomy without compromising safety.
See also: bookkaru
Frequently Asked Questions
How Do Multi-Chain Wallets Handle Gas Fees Across Chains?
Gas fee models vary by chain and bridge, with some using preserved base fees and others adaptive pricing; cross-chain reliability depends on relays and bridges. The system balances costs, security, and user freedom for cross-chain operations.
Can I Recover Funds if a Wallet Seed Is Compromised?
Like a careful compass, the answer is no: recoverability depends on seed compromise. If seed compromised, recovery procedure is compromised; cross chain compatibility may fail. Audit coverage matters; potential funds loss requires rapid, vigilant action. Freedom demands caution.
What Are Cross-Chain Transaction Speeds and Reliability Benchmarks?
Cross-chain transaction speeds vary; average cross chain latency ranges from seconds to minutes depending on networks and congestion, while cross chain reliability hinges on security guarantees and bridging protocols. The assessment remains risk-aware, structured, and freedom-focused.
Do Multi-Chain Wallets Support Non-Evm Blockchains?
Despite devout optimism, some multi-chain wallets offer non EVM compatibility; others do not, varying by project. They aim for cross chain wallets support, balancing risk and freedom while detailing limitations of non-EVM blockchains.
How Do Audits Address Potential Multi-Chain Security Gaps?
Audits address potential multi-chain security gaps by evaluating cross chain risks and verifying audit methodologies; they identify entry points, control weaknesses, and mitigations, ensuring transparent risk judgments while preserving user autonomy and informed decision-making across diverse ecosystems.
Conclusion
In an old harbor of many ships, a single lighthouse guides vessels from different seas. The multi-chain wallet stands as that beacon, coordinating tides, currents, and signals across networks. Yet missteps—shallow vaults, brittle bridges, or opaque governance—bite like sudden squalls. The prudent captain keeps keys private, checks routes, and rehearses aborts, knowing risk travels with every voyage. With disciplined custody, cross-chain journeys become safer, more predictable, and navigable by a steady hand and vigilant watch.